Five services. One integrated security program.
Every engagement starts with understanding your business — not selling you a product. We buildsecurity programs that fit your operations, your risk profile, and your budget. Then we run them foryou.
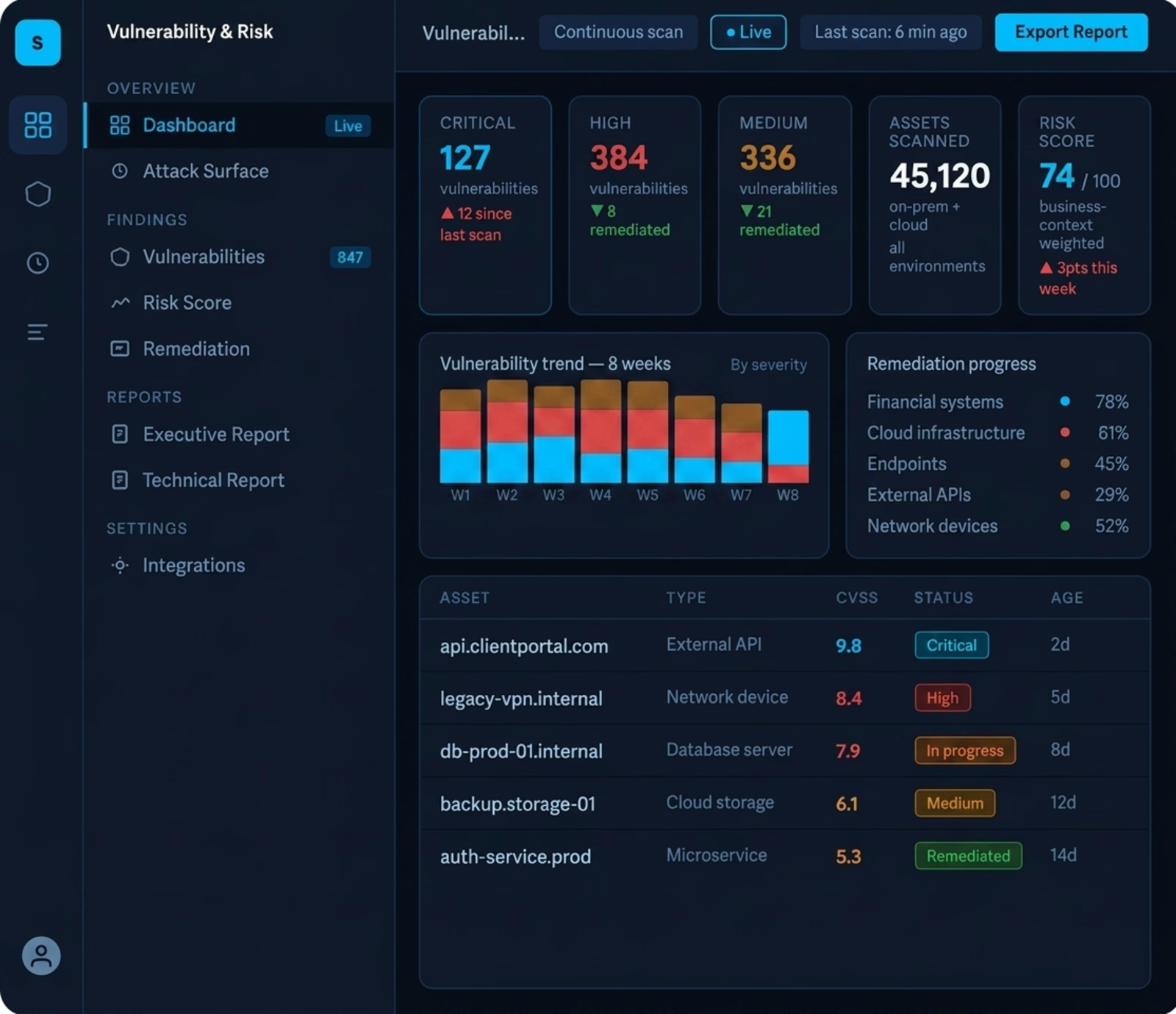
Know where you are exposed. Fix what matters most.
Most organizations are not short on security tools. They are short on clarity — not knowing which vulnerabilities actually put the business at risk, and which findings can wait. We solve that. Our Vulnerability & Risk Management program does not hand you a list of 4,000 findings and walk away. We analyze your environment in the context of how your business operates, score risk by real-world business impact, and give you a clear, prioritized roadmap your team can actually execute.
What makes our approach different
We start by understanding your business operations before scanning a single asset — so findings are ranked by what actually matters to you, not generic CVSS scores
We translate technical findings into executive language — your CFO and board understand the risk, not just your IT team
We build the program around your reality — your team size, your budget, your compliance requirements
Continuous coverage, not point-in-time snapshots — you always know your current exposure
Delivered to
Financial services firms managing regulatory exposure across multiple jurisdictions
Energy and manufacturing companies with complex, distributed environments
Organizations preparing for SOC 2, ISO 27001, PCI-DSS, or NIST audits
What you get
Continuous vulnerability scanning across your full attack surface
Business-context risk scoring — not just severity ratings
Executive summary + technical report, updated on your schedule
Remediation roadmap with prioritized, actionable guidance
Validation retesting to confirm fixes are effective
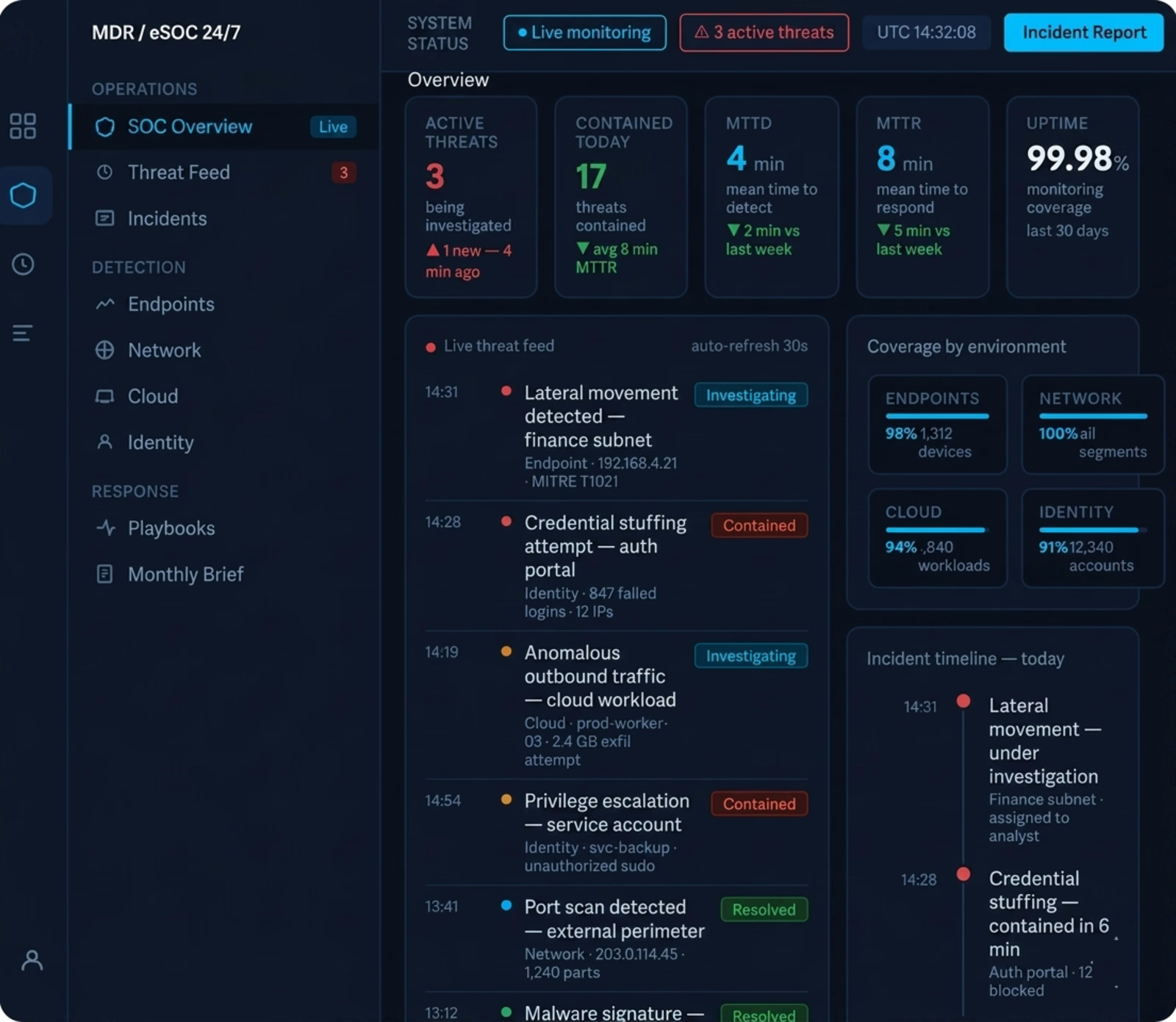
24/7 eyes on your environment. No SOC required on your end.
Building an internal security operations center costs millions and takes years. Most organizations —even large ones — cannot justify it. Scyre’s managed eSOC gives you the same level of coverage at a fraction of the cost, with none of the infrastructure overhead. We monitor your environment around the clock, detect threats in real time, and respond on your behalf — so your team can focus on running the business.
What makes our approach different
We act, not just alert — when a threat is detected, we contain it. We do not send you a ticket to investigate on your own
No local infrastructure required — our delivery model is 100% remote, designed for organizations across United States, Latin America, Europe, and the Middle East where on-site vendor presence is not practical
Programs built around your environment — not a one-size-fits-all sensor deployment that ignores how your business actually operates
We have stood up complete MDR programs for financial institutions with zero prior detection capability — from contract to live coverage in weeks, not months
Delivered to
Banks and financial institutions requiring 24/7 threat visibility with no internal SOC
Organizations that have experienced an incident and need immediate, professional coverage
Companies expanding into new markets who cannot afford gaps in security coverage
What you get
24/7 monitoring across endpoints, network, cloud, and identity environments
Real-time threat detection and active containment — minimizing dwell time
Incident response support and detailed post-incident reporting
Monthly executive threat briefings in plain language
Full remote delivery — no hardware, no on-site visits required
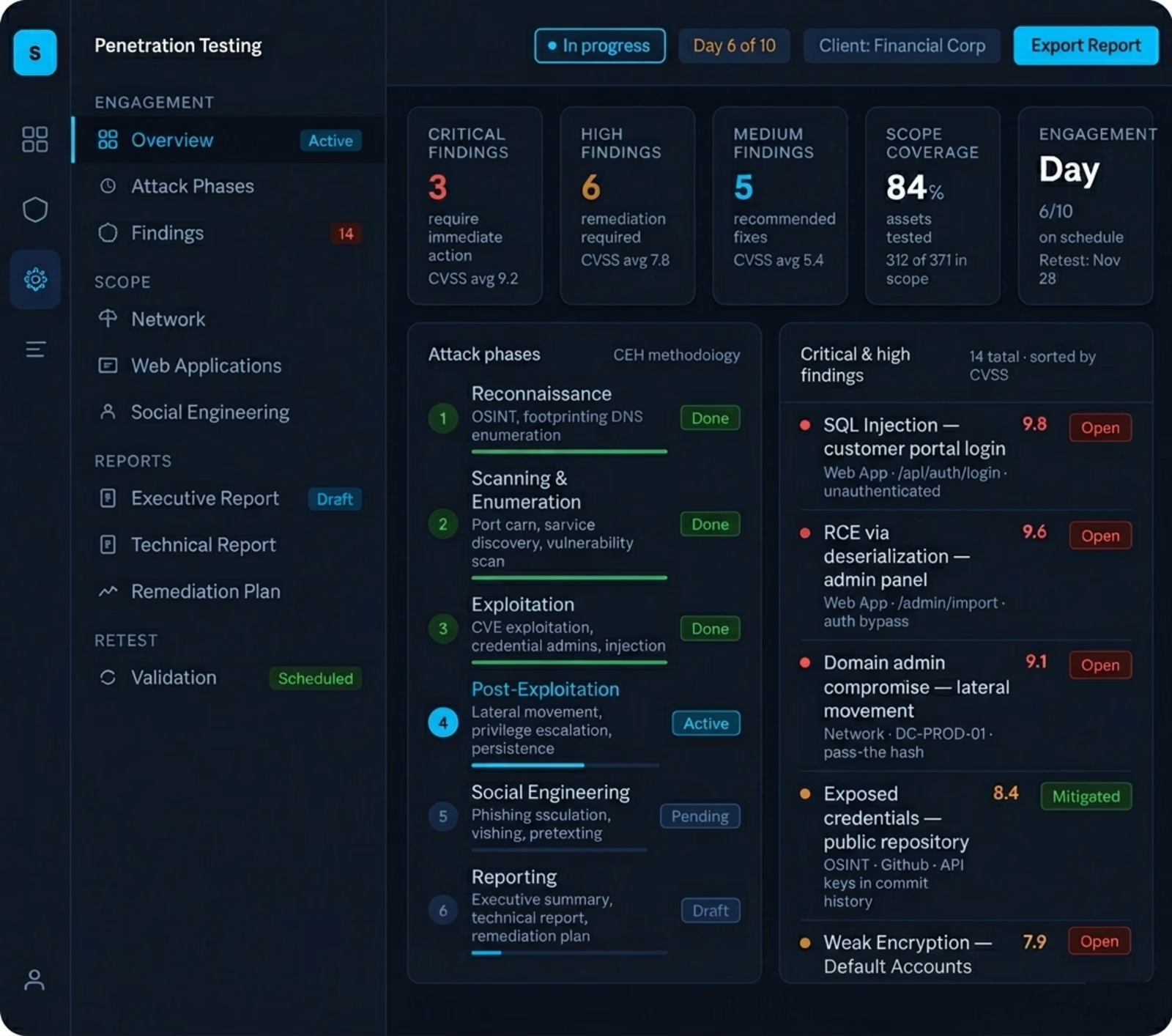
Find your gaps before an attacker does — with findings your leadership actually understands.
A penetration test is only valuable if the findings drive action. Too many reports end up in a drawer because the results are too technical for leadership to act on, or too generic to be prioritized. Scyre’s penetration testing program delivers something different: a structured simulation of real attack scenarios, with findings rated by business impact — not just CVSS score — and a clear remediation plan your team can execute immediately.
What makes our approach different
Every engagement starts with a scoping conversation about your business — not a standard questionnaire. We understand what you are protecting before we start probing
Findings are rated by business impact, not just technical severity — your CFO understands the risk, not just your security team
We do not just find the problem — we tell you exactly how to fix it, in order of priority
Retest included — we validate that your team actually closed the gaps we identified
Delivered to
Financial institutions required to demonstrate security posture for regulatory compliance
Organizations preparing for SOC 2 Type II, PCI-DSS, or ISO 27001 certification
Companies that have never had an independent security assessment and want to know where they truly stand
What you get
Network, web application, and social engineering testing scoped to your environment
Executive summary written for non-technical leadership — risk in business language
Technical report with step-by-step remediation guidance per finding
Certified testers: CEH, OSCP, CISM
Retest included to validate remediation effectiveness
Compliance-ready documentation: PCI-DSS, SOC 2, ISO 27001
Your organization has a digital footprint far beyond what you control. We map it — and protect it.
Most security programs focus on what is inside the perimeter. But your real exposure often lives outside it — leaked employee credentials circulating on dark web forums, counterfeit domains designed to phishyour clients, or executive profiles being impersonated on social media. By the time you find out, thedamage is done. Our Cyber Exposure & Brand Protection service gives you continuous visibility into yourexternal attack surface — before adversaries can weaponize what they find
What makes our approach different
We monitor what adversaries actually see — your exposed assets, leaked data, and impersonation attempts — not just what is inside your firewall
Particularly critical for financial institutions: credential leaks and brand impersonation in the financial sector are among the fastest-growing attack vectors in United States, Latin America, Europe, and the Middle East
When we find something, we do not just alert you — we support the takedown and remediation process
Continuous monitoring means you are never caught off guard by exposure that has been building for months
Delivered to
Banks and financial institutions protecting client trust and regulatory standing
Organizations with public-facing brands operating in multiple markets
Companies with distributed workforces where credential hygiene is difficult to control
What you get
Dark web and deep web monitoring for leaked credentials and sensitive data
Brand impersonation and counterfeit domain detection
Attack surface mapping — a clear view of what adversaries see from outside your perimeter
Takedown support for fraudulent assets and impersonation profiles
Continuous monitoring with prioritized alert-based reporting

Your applications are running. Attackers are testing them right now.
Web applications and APIs are the most targeted attack surface in modern organizations — and most security programs treat them as an afterthought. DDoS floods take services offline in minutes. Automated bots probe your login pages, abuse your APIs, and execute fraud at scale. Zero-day exploits bypass traditional defenses before patches are even available. Application Shield delivers enterprise-grade protection across all these vectors — continuously, automatically, and without requiring your team to manage complex rule sets or react to every alert.
What makes our approach different
Full-spectrum coverage from a single program — DDoS mitigation, WAF, bot management, and API protection working together, not as disconnected tools
AI-powered threat detection that adapts in real time — zero-day attacks and novel threats are blocked automatically, without waiting for manual rule updates
Minimal false positives — your legitimate users and business traffic are never disrupted by overly aggressive blocking
Real-time visibility with a dedicated portal — your team sees what is happening, what was blocked, and why, at any moment
Fully managed — we handle configuration, tuning, threat intelligence updates, and 24/7 response so your team can focus on running the business
Delivered to
Any organization with public-facing web applications, customer portals, or APIs — regardless of industry
Financial institutions and e-commerce platforms where application availability and fraud prevention are business-critical
Government agencies and enterprises with compliance mandates that require demonstrated application security controls
Organizations that have been hit by a DDoS attack, bot abuse, or application-layer breach and need immediate, professional protection
What you get
DDoS protection — network and application layer, including volumetric, protocol, and encrypted attack mitigation
Web Application Firewall (WAF) — blocks OWASP Top 10, injection attacks, XSS, and application-layer exploits
Bot management — distinguishes legitimate traffic from scrapers, credential stuffers, and automated fraud tools
API security — automated API discovery, schema validation, and protection against API-specific threats
Zero-day protection via machine learning — threats blocked before signatures exist
Real-time attack analytics and executive reporting — mean time to resolve (MTTR), attack distribution, and trend analysis
Fully managed service — no rules to write, no infrastructure to maintain, no expertise required on your end

Not sure which service fits your situation?
Start with a 20-minute discovery call. We will ask the right questions, listen carefully, and tell you where we think you should focus first — with no obligation.

